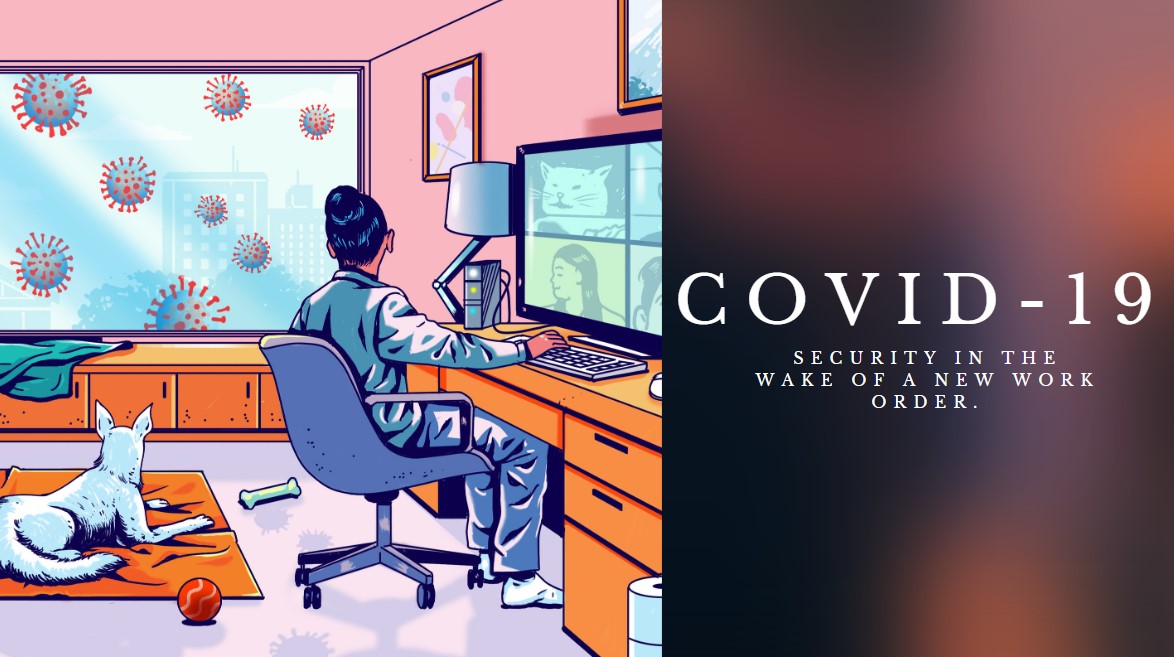
In the Wake of a New Work Order
COVID-19 is rapidly changing how we work, communicate, and interact with one another. Some private companies, public institutions, and government agencies are mandating that all employees who can, must work from home.
This is causing a major challenge for IT and security teams around the globe. Few Managements and CISOs had planned for such a rapid switch over to a full remote workforce. Network topologies radically shifted, adding home broadband access points and routers that were never designed for enterprise-grade security and management. Many employees have had to use their own laptops and PCs to keep working which generally lack the types of security controls that IT teams always place on company-issued devices.
This also creates an environment which becomes a soft target for adversaries where a number of attack types could be easier to execute including drive-by downloads, phishing, exploits of VPN vulnerabilities, malware propagation, and exploits of home network routing equipment (as many are going to be using routers from mobile network operators and modem from Internet Companies) or connected unsecured IoT devices as employees continues to work from home.
For many users this is the first time they have worked from home. Not only is there the stress of the uncertainties around COVID-19 but also an adjustment period for people transitioning their work habits to home as they tend to be less alerted and easily distracted but for the adversaries and threat actors we are protecting ourselves from, working remotely has been a culture from time immemorial.
Many organizations in Nigeria understand what downtime in services and risk of working from home could cause them, so they took drastic measure by housing their essential team (mostly IT and security team) in a place with close proximity to their physical offices. And other organizations who are not prepare and do not have facilities that can ensure secure remote working environment if they have to move 60% of their workforce to suddenly work from home also took the same step.
Business are shifting priorities to stay afloat as COVID-19 affects every area of corporate work amidst lock-down, employees will continue to work from home to maintain normal business operations but following the below listed cybersecurity measures will help both employees and businesses to do it securely and minimize all risk to near-zero.
-
Need for employees training on security.
When it comes to security, technologies don’t just do it. There is always need for the people who are involved in the operation of the business processes. It is key that these employees are informed enough on the various ways’ hackers would victimize new work from home employees. CISOs must review and validate their security strategy and as well take extra precautions on their risk tolerance level.
-
Use a reliable Virtual Private Network (VPN)
A virtual private network will really be of great importance in this period of pandemic. As it gives a secure remote access to organization’s servers as if they are directly connected to the network. It simply creates a virtual connection to the organization’s network for employees to continue with normal work activities. Validate VPN security, capacity and throughput
-
Subscribe to an MSSP
Subscribing to an MSSP has never been more important both for small and large organizations than in this time of pandemic. It becomes the sole aim of the MSSP to monitor and protect their network and endpoints 24/7 such that organization can focus on their key business processes while they work from home.
-
Restrict Unnecessary Office Visit
One cannot write off the chances of adversaries from taking the hack to site which make physical office security to be a high risk in this period of pandemic. Some IT workers may have to come to work to fix problems. This, should be avoided as much as possible for safety concerns especially when its just a minor problem. With everyone aware of work from home policies, take extra precautions with physical security.
In Conclusion
It is important for both the employees and the business owners to play their roles during this period. Knowing fully well that the larger chunk of this task rest on the shoulder of the Security and IT Teams which are meant to review and validate all security controls in place and closely monitor all activities coming from employees working remotely. Simulation of attacks is a way to ensure all the new security validations and configurations are working as expected.
Authors
Hamzah ‘Lateef and Chukwuka Isaac