They lure their victims with the bait of a seemingly innocent email or landing page in an attempt to steal their user credentials. And they only need to succeed once to get in.
Once they have hooked their victim, a cybercriminal can take over an entire network in a matter of minutes. Or worse yet, they can lurk quietly on a connected device for months, unbeknownst to the IT team, plotting how to extract the most profit and/or disrupt the now compromised network.
We care about this seemingly inconsequential phishing lures because once a hacker has a foothold on your network, they can exploit it to infiltrate deeper into your systems and cause significant harm.
Using a variety of Tactics, Techniques, and Procedures (TTP), the hacker will succeed – whether it’s ransom, theft, or a more sinister type of attack – it’s only a matter of time before they will get exactly what they want.
The infographic below illustrates how simply an attack starts, and how persistent an attacker can be once inside your network.
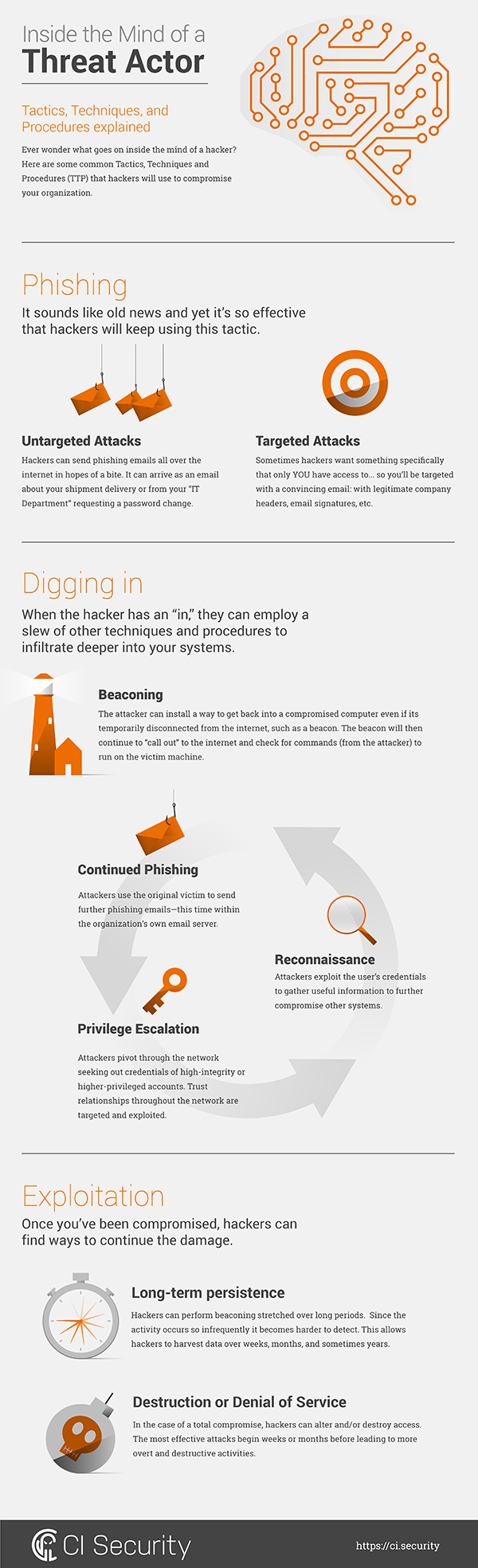
Phishing Is the Entry Point
You may think of phishing as some old-timey Nigerian Prince scam that only works on your grandma, but the attack vector has become wildly sophisticated and widely successful since its inception in the 1990s.
While certainly not the only tactic in the cyber criminal’s toolkit, phishing scams are the easiest and most effective way to gain access to a network or obtain personal information.
The FBI recently warned of a 270 per cent increase in identified victims and exposed loss from the business e-mail compromise scams. According to the data collected, law enforcement received reports from 17,642 victims in every U.S. state and in at least 79 countries, which amounted to more than $2.3 billion in losses between October 2013 and February 2016. It’s not just grandma falling for the things.
VIPs Are Walking Targets for Spearphishing
Let’s just start with spearphishing. If an attacker is spearphishing you, it’s a targeted attack that’s looking for something you have. Your login credentials, your HR privileges, your bank account number, whatever. Spear phishers aren’t just spraying untargeted Nigerian Prince scams out to some email list they bought—they’re looking for something specific you have and tailoring the message to you. And when crafted with skill, the emails they send will appear much more authentic than whatever lands in your spam box on the daily.
Whale phishing, or whaling, is the practice of marking CEOs and other high-value targets. Board members — with high levels of trust and names that carry weight inside their respective organizations — are increasingly targeted.
Regardless of the target (or lack thereof), hackers will often disguise malware inside Office documents (macros), encrypted zips, or even “password reset pages.”
There are gobs of pre-built phishing kits available on the dark web, so even relatively unskilled threat actors can look like pros.
Tactics, Techniques, and Procedures (TTP) Executed after the Breach
So, who cares if someone got the email login credentials for Jeff from Accounting or Admin privileges to the printer on Floor 6, you might ask.
We care about these phishing incidents because once a hacker obtains credentials, there is nothing to stand in the way of the threat actor. Access from an unprivileged account is sufficient to begin the job of getting administrative access, after which he/she will have full clearance to do their worst to get your best, most valuable, assets and data. Furthermore, the actor can lurk for months, exploring internal systems, and then carefully extracting valuable treasures residing deep within the network.
Here are just a few post-breach TTP:
Attackers can use beaconing to get back into a compromised computer. The installed beacon will “call out” to the internet and check for commands from the attacker.
With a logged-in user’s credentials, attackers can use reconnaissance to gather useful information to further compromise other systems. Often the goal is access to local admin and/or domain admin accounts.
Continued Phishing
Once attackers have compromised Jeff from Accounting’s email account, they can use it to send further phishing emails, this time from within the organization’s email server.
Long-Term Persistence
Hackers can perform beaconing stretched out over long periods. Since the activity occurs so infrequently, it’s harder to detect. This allows hackers to harvest data over weeks, months, and sometimes years.
Destruction or Denials of Service
In the case of a total compromise, hackers can alter and/or destroy access. The most effective attacks begin weeks or months before leading to more overt and destructive activities.
Phishing Tactics Continue to Evolve
But no one is going to fall for the old Nigerian Prince scam anymore, right…? Wrong! As soon as the old tricks quit working, cybercriminals get creative and employ a new trick to get the same, predictable outcome. One upcoming escalation is the implementation of artificial intelligence by threat actors for more surgical targeting, and crafting better ”bait”.
The numbers can be murky because companies aren’t required to report such compromises, and therefore have no incentive to broadcast to the world when a malicious actor gets into their systems. And while it’s best to scrutinize stats offered by organizations that peddle anti-phishing solutions, it’s also best to recognize that the problem is real and take steps to shore up your defences.
The truth is that as long as humans are opening emails, phishing will continue to be an effective tactic for the foreseeable future.
How to Protect Your Business from Phishing Attacks
Wondering how to protect your business against all this nastiness? The FBI offers this handy shortlist of best practices for businesses who want to fend off phishing attacks:
- Be wary of email-only wire transfer requests and requests involving urgency
- Pick up the phone and verify legitimate business partners
- Be cautious of mimicked email addresses
- Practice multi-factor authentication
Lastly, note that many of the TTP employed will create a signal on the network, which can be teased out of the aggregated intrusion detection, log, and other events, using analytics that employs statistical, frequency, signature, reputation, and other methods. We all have to assume that periodic compromises will occur and that to the greatest extent, they will be caused by user action. If you detect and put out the stove fire quickly, the house will not be engulfed and your records, finances, and critical services will have no impact.









Hazırlanan metraj ve yaklaÅık maliyet raporları sonucu teklif oluÅturma aÅamasında da firmamız söz konusu iÅ ile alakalı olarak firmanızın istemesi durumunda teknik destek konusunda her aÅamada yardımcı olmaktadır.
Alright.
very informative articles or reviews at this time.
Hi Muhasebe. Thank you so much. I really appreciate this.
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information.
Thank you very much for your kind words and bookmarking our site. I really appreciate this.
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
Thank you so much for appreciating my contents and reading as well. i sincerely hope it inspires more people in your network.
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!
Hi Ronald. I am glad you like my content.Thank you so much for sharing with your network as well. I hope they would also be inspired by my contents.
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
Hi Kamari. Thank you so much. I am glad the article my article was helpful.
I just like the helpful information you provide in your articles
Thank you so much. I am glad the information was helpful.
Nice post. I learn something totally new and challenging on websites
I like the efforts you have put in this, regards for all the great content.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
Thank you for visiting and reading. I am glad it was helpful.
Thank you Andre. I am glad it was helpful.
There is definately a lot to find out about this subject. I like all the points you made