Like we always state, a cyberattack never goes outdated, it only evolves with the trend and technological advancement. In August, KrebsOnSecurity warned that scammers were contacting people and asking them to unleash ransomware inside their employer’s network, in exchange for a percentage of any ransom amount paid by the victim company. In November, Authorities in Nigeria arrested a suspect in connection with the scheme — a young man who said he was trying to save up money to help fund a new social network.
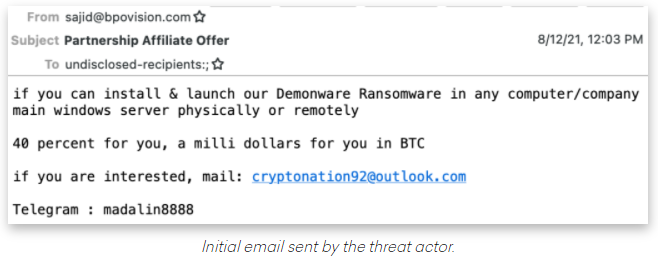
The brazen approach targeting disgruntled employees was first spotted by threat intelligence firm Abnormal Security, which described what happened after they adopted a fake persona and responded to the proposal in the screenshot above. “According to this actor, he had originally intended to send his targets—all senior-level executives—phishing emails to compromise their accounts, but after that was unsuccessful, he pivoted to this ransomware pretext,” Abnormal’s Crane Hassold wrote.
Abnormal Security documented how it tied the email back to a Nigerian man who acknowledged he was trying to save up money to help fund a new social network he is building called Sociogram. Reached via LinkedIn, Sociogram founder Oluwaseun Medayedupin asked to have his startup’s name removed from the story, although he did not respond to questions about whether there were any inaccuracies in Hassold’s report. “Please don’t harm Sociogram’s reputation,” Medayedupin pleaded. “I beg you as a promising young man.”
After he deleted his LinkedIn profile, I received the following message through the “contact this domain holder” link at KrebsOnSecurity’s domain registrar [curiously, the date of that missive reads “Dec. 31, 1969.”]. Mr. Krebson is a clout-chasing monger.
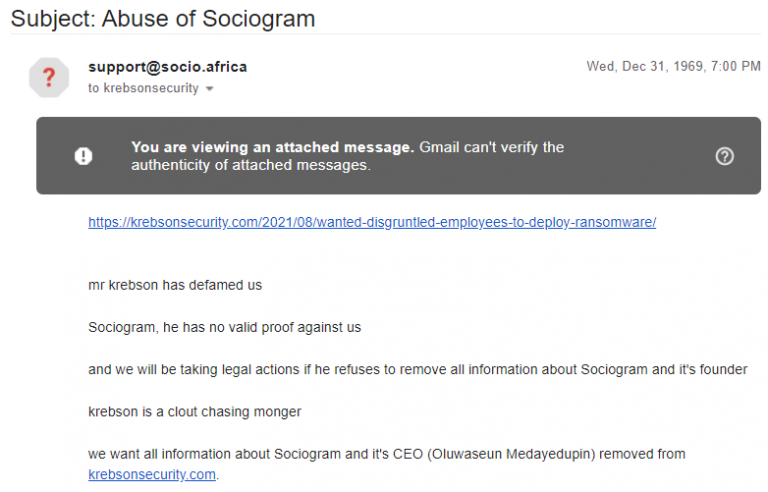
Mr. Krebson also heard from an investigator representing the Nigeria Finance CERT on behalf of the Central Bank Of Nigeria. While the Sociogram founder’s approach might seem amateurish to some, the financial community in Nigeria did not consider it a laughing matter. At the end of that week, Nigerian police arrested Medayedupin. The investigator says formal charges will be levied against the defendant sometime that week in November. KrebsOnSecurity spoke with a fraud investigator who is performing the forensic analysis of the devices seized from Medayedupin’s home. The investigator spoke on the condition of anonymity out of concern for his physical safety.
The investigator — we’ll call him “George” — said the 23-year-old Medayedupin lives with his extended family in an extremely impoverished home, and that the young man told investigators he’d just graduated from college but turned to cybercrime at first with ambitions of merely scamming the scammers. George’s team confirmed that Medayedupin had around USD 2,000 to his name, which he’d recently stolen from a group of Nigerian fraudsters who were scamming people for gift cards. He admitted to creating a phishing website that tricked a member of this group into providing access to the money they’d made from their scams.
Medayedupin reportedly told investigators that for almost a week after he started emailing his ransom-your-employer scheme, nobody took him up on the offer. But after his name appeared in the news media, he received thousands of inquiries from people interested in his idea. George described Medayedupin as smart, a quick learner, and fairly dedicated to his work. “He seems like he could be a fantastic [employee] for a company,” George said. “But there is no employment here, so he chose to do this.”
What’s interesting about this case — and indeed likely why anyone thought this guy worthy of arrest — is that the Nigerian authorities were fairly swift to take action when a domestic cybercriminal raised the specter of causing financial losses for its banks. After all, the majority of the cybercrime that originates from Africa — think romance scams, Business Email Compromise (BEC) fraud, and unemployment/pandemic loan fraud — does not target Nigerian citizens, nor does it harm African banks. On the contrary: This activity pumps a great deal of Western money into Nigeria.
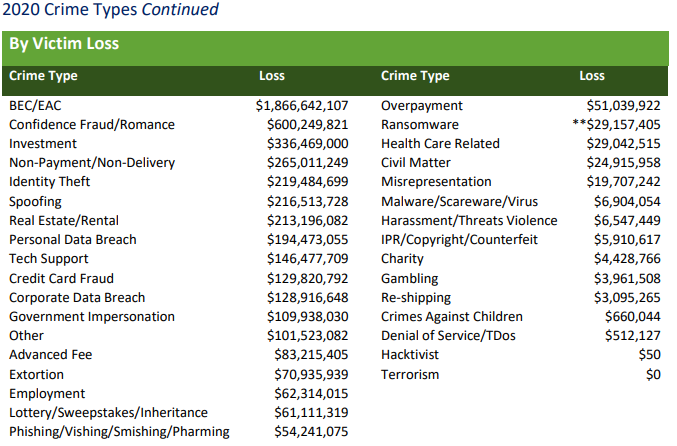
How much money are we talking about? The financial losses from these scams dwarf other fraud categories — such as identity theft or credit card fraud. According to the FBI’s Internet Crime Complaint Center (IC3), consumers and businesses reported more than $4.2 billion in losses tied to cybercrime in 2020, and BEC fraud and romance scams alone accounted for nearly 60 percent of those losses.
If the influx of a few billion US dollars into the Nigerian economy each year from cybercrime seems somehow insignificant, consider that (according to George) the average police officer in the country makes the equivalent of less than USD 100 a month.
Ronnie Tokazowski is a threat researcher at Agari, a security firm that has closely tracked many of the groups behind BEC scams. Tokazowski maintains he has been one of the more vocal proponents of the idea that trying to fight these problems by arresting those involved is something of a Sisyphean task, and that it makes way more sense to focus on changing the economic realities in places like Nigeria.
Nigeria has the world’s second-highest unemployment rate — rising from 27.1 percent in 2019 to 33 percent in 2020, according to the National Bureau of Statistics. The nation also is among the world’s most corrupt, according to 2020 findings from Transparency International.
“Education is one piece, as raising awareness is hands down the best way to get ahead of this,” Tokazowski said, in a June 2021 interview. “But we also need to think about ways to create more business opportunities there so that people who are doing this to put food on the table have more legitimate opportunities. Unfortunately, thanks to the level of corruption of government officials, there are a lot of cultural reasons that fighting this type of crime at the source is going to be difficult.”
Conclusion
Please permit me to either bore you or sweep you off your feet with a few biochemistry lines. Bitter employees seem to be the bone of contention in this Enzyme and its active site model. The threat actor represents the enzyme, while the employee represents the active site of the enzymatic action. The onlooker is the employer, who cannot see through an endless mirage of the bitterness of an employee but can either induce or inhibit the reaction. Employers should be very cautious and apply security measures that minimize their chances of falling prey to such evolutionary attacks.









