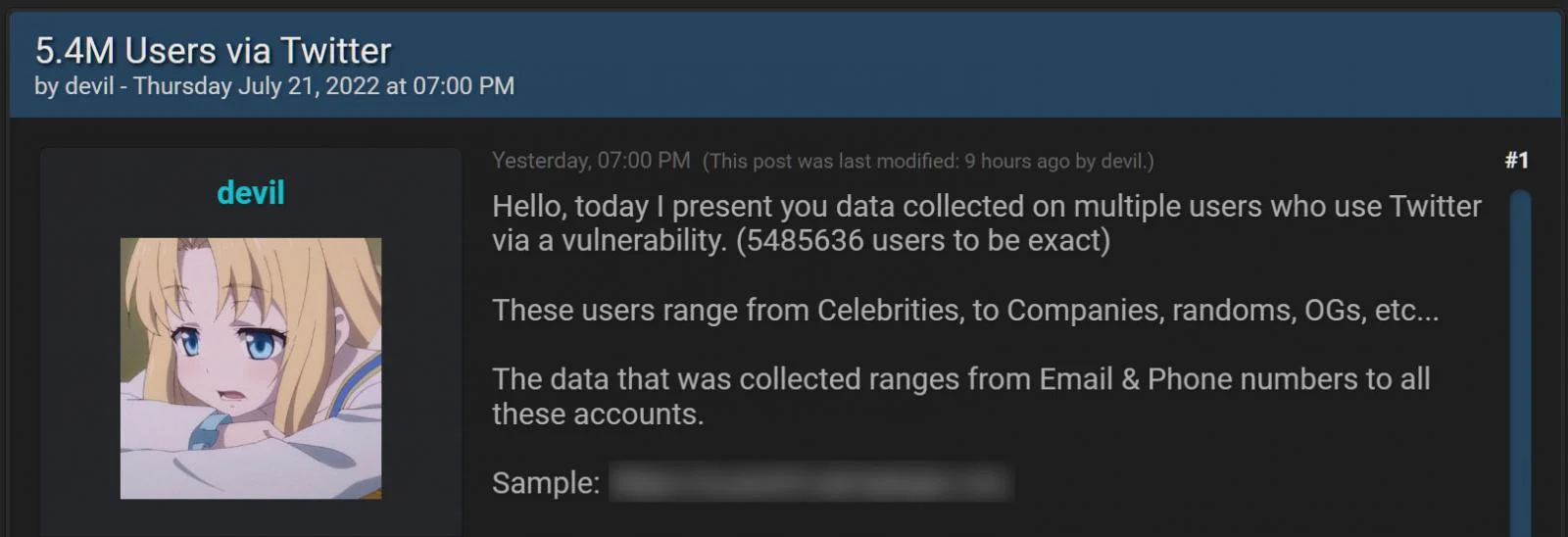
Twitter on Friday informed users of a security bug that had allowed “a bad actor” to obtain and sell the personal data of account holders. The tech giant did not provide the number of compromised accounts, but media reports state that more than five million users could have been affected. A company statement said that the system vulnerability, which resulted from a June 2021 code update, made it possible to enter an email address or phone number and learn if either was linked to a specific account. The company said at the time that it had no evidence of a malicious individual using this exploit, but that changed in July 2022 when it was reported that information about over 5.4 million accounts was being sold on a hacker forum. This was as a result of a now-patched zero-day vulnerability allowing the threat actor to compile user account profiles—5485636 users to be precise.
This includes accounts of people who would rather keep their information pseudonymous, such as whistleblowers and celebrity accounts.
The company vowed to contact the owners of the accounts that were affected by the “unfortunate” incident. However, Twitter admitted that it had been impossible to confirm every account that was potentially compromised. Although passwords were not exposed, Twitter came up with a set of recommendations to protect accounts. The owners of pseudonymous accounts have been warned against adding publicly known phone numbers or email addresses, while all users are advised to enable two-factor authentication to protect their data. When reached by RestorePrivacy, this hacker, who was operating under the username “devil,” revealed that he was asking for at least $30,000 for the database, which he stressed he managed to gather due to “Twitter’s incompetence.” He said that the exact mechanism of how he took advantage of the bug was explained in the January report of the HackerOne website by user “Zhirinovsky,” who was the first to warn Twitter of the vulnerability. Twitter thanked “Zhirinovsky” for “helping keep Twitter secure” and awarded him a $5,040 bounty for his investigation.
Even though most of the data being sold is publicly available, threat actors can use the email addresses and phone numbers in targeted phishing attacks. All Twitter users should be vigilant when receiving emails from Twitter, especially if they ask you to enter login credentials, which should only be done on Twitter.com.








